Welcome in last episode of first season of Offensive OSINT. Today's topic is very important from ethical perspective and super interesting from technical point of view. This is the field where Open Source Intelligence is used the most. We will go through most common methods of human trafficking online, how to detect possible cases and where it takes place.
Last article about leak hunting is accessible below

Introduction
Human trafficking is a very serious and worldwide problem, for example only in 2016 around 4 millions people were victims of sex trafficking. It's also very profitable business - $150 billion a year for traffickers, $99 billion of which comes from commercial sexual exploitation. Of course, it's only estimation because it is not possible to give exact digits due to hidden nature of these activities. Most of the victims are woman forced into sexual exploitation and marriage. Other most vulnerable groups are children, also mostly for sexual abuse, and man for labors or organs.
Full report about modern slavery you can find below
https://www.ilo.org/wcmsp5/groups/public/@dgreports/@dcomm/documents/publication/wcms_575479.pdf
https://www.stopthetraffik.org/about-human-trafficking/the-scale-of-human-trafficking/
It's hard to spot human trafficking in real live as well as online. The Techniques, Tactics & Procedures used by perpetrators make any online advertisement look innocent on first sight. When first ad with victim has been posted the game starts, if law enforcement and private companies can detect possible human trafficking on this stage, then there will be smaller chance that victim will be exploited later. However detection of this is incredibly hard, how can you spot the difference between common escort service advertisement and possible human trafficking victim?
But let's start from the beginning, where these ads are posted and what this is about.
OSINT & HUMAN TRAFFICKING
For those who follow this topic and are interested in general cybercrime, I don't need to introduce Backpage - the classified ads service that has been seized by FBI with cooperation of criminal unit of IRS and USPS over accusation of promoting human trafficking and prostitution.

Long story short is that they were accused of:
- Editing ads both manually and automatically, to hide true nature of the advertisement.
- Being aware about conducted activities i.e. prostitution, human trafficking, on the website.
- Shady corporate structure
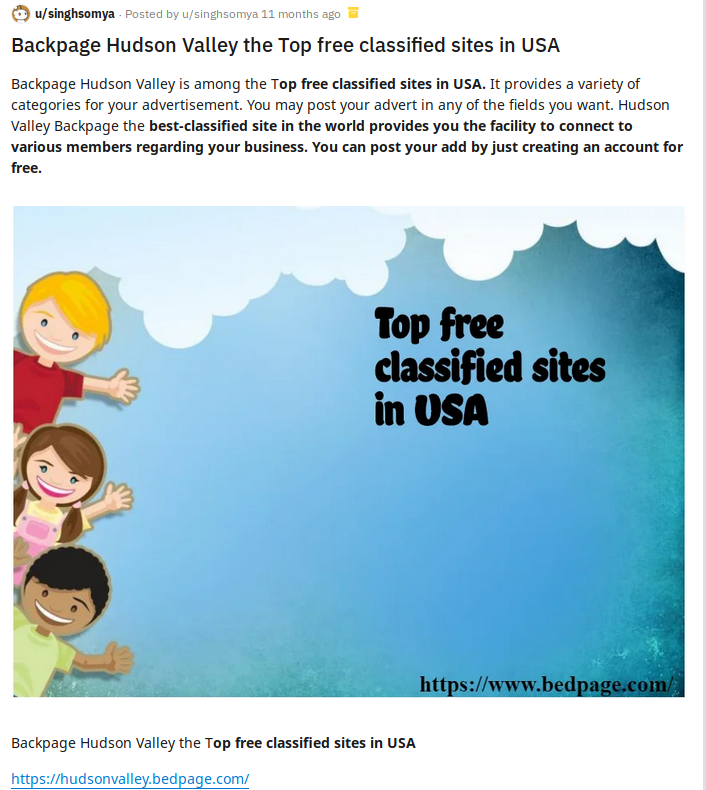
Indictments include many interesting topics in investigation and couple horrible statistics regarding human trafficking and Backpage. For example moderators of Backpage manually reviewed every ad and changed forbidden words related to prostitution and sexual exploitation to clear ones and posting ad after that.
They also hide details about ads and real numbers from NCMEC (National Center for Missing and Exploited Children). Only in January 2012 Backpage reported 508 ads to NCMEC, which is 16 everyday, imagine the scale.
Backapge was aware what is going on but tried to hide it and make money at the same time. They were even coaching users how to post clean ads so it won't be deleted.
Filters and methods used by them were not enough to detect and fight with prostitution and human trafficking.
Accusation list is longer and presented in more details in the documents that are beautiful read for every one who is interested in OSINT and cybercrime.
https://www.hsgac.senate.gov/imo/media/doc/Backpage Report 2017.01.10 FINAL.pdf
https://courts.illinois.gov/R23_Orders/AppellateCourt/2019/1stDistrict/1190619_R23.pdf
https://digitalcommons.law.scu.edu/cgi/viewcontent.cgi?article=2771&context=historical
http://archive.azcentral.com/persistent/icimages/news/backpage%20indictment.compressed.pdf
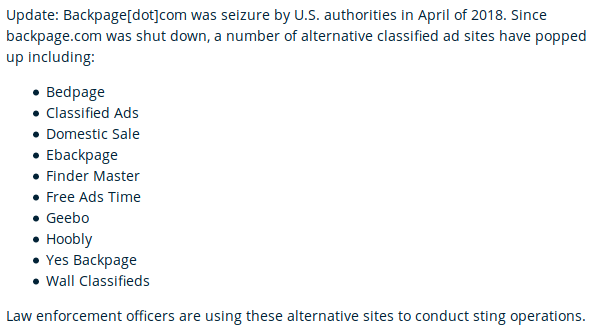
It was really quick summary about Backpage which is gone since April 2018. Universe does not like emptiness so many similar pages appeared after Backpage has been seized. To introduce you world of human trafficking we have to find Backpage-like websites and distinguish real from fake ones. I found that many BP clones belong to one Indian company and it's used to promote only fake advertisements.
Diving into origins of Bedpage & afterdarkads & eBackpage
All domains of Backpage are not accessible anymore, you can find only indexed google pages and entries from wayback machine.
To find some of the suspicious ads try duckduckgo or google dork - site:backpage.com "forbidden_word"
Even during Backpage lifetime, many clone sites appeared with same design and similar name like yesbackpage, ibackpage, ebackpage, Bedpage and other like afterdarkads.
So far I was able to identify following backpage-like domains:
yesbackpage
ibackpage
ebackpage
icracker (for Australia)
2backpage.com
and probably many many others, but it's not the point right know to find all of them. I can state with high confidence that these sites belong to web design company - Argalon, operating from Indore, India.
Some of the domains contain mostly spam and fake advertisements with referral links to other dating or porn sites.
Exhibit A
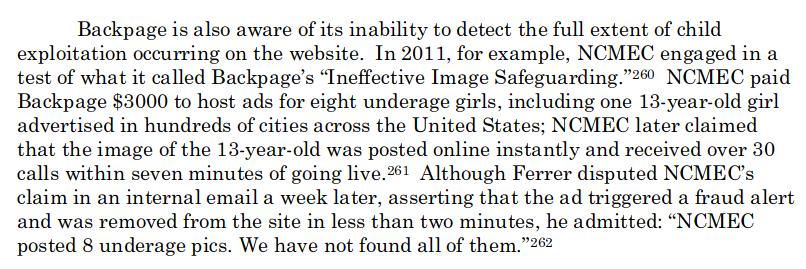
website ibackpage.com was owned by employee of Argalon since at least 2016. Literally couple days ago, whois record has been anonymized.
Exhibit B

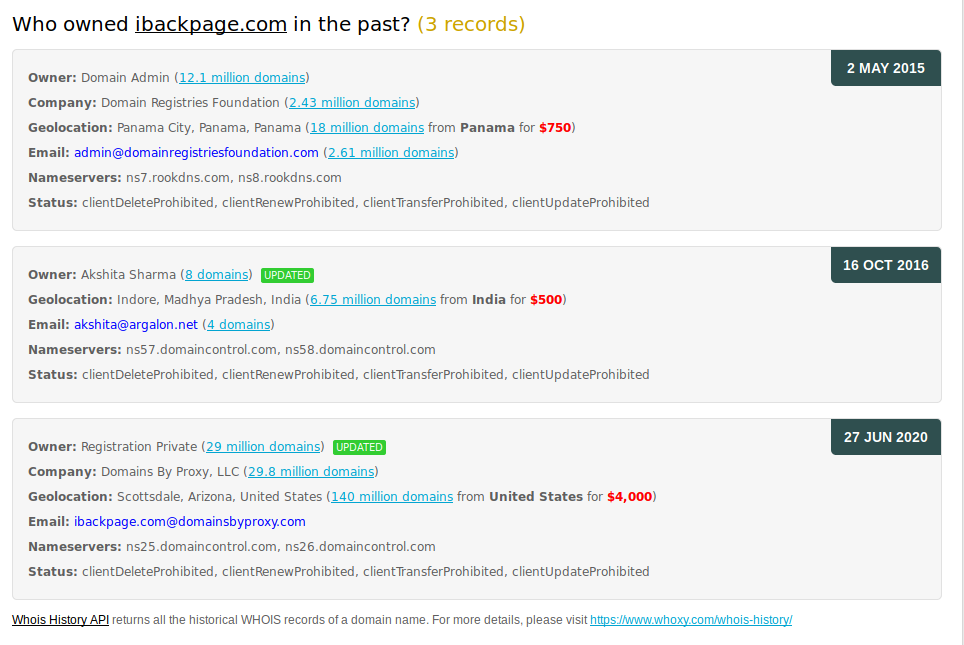
Owner of argalon.net going by name Prashant Shinde is associated with many other domains related to classified ads.

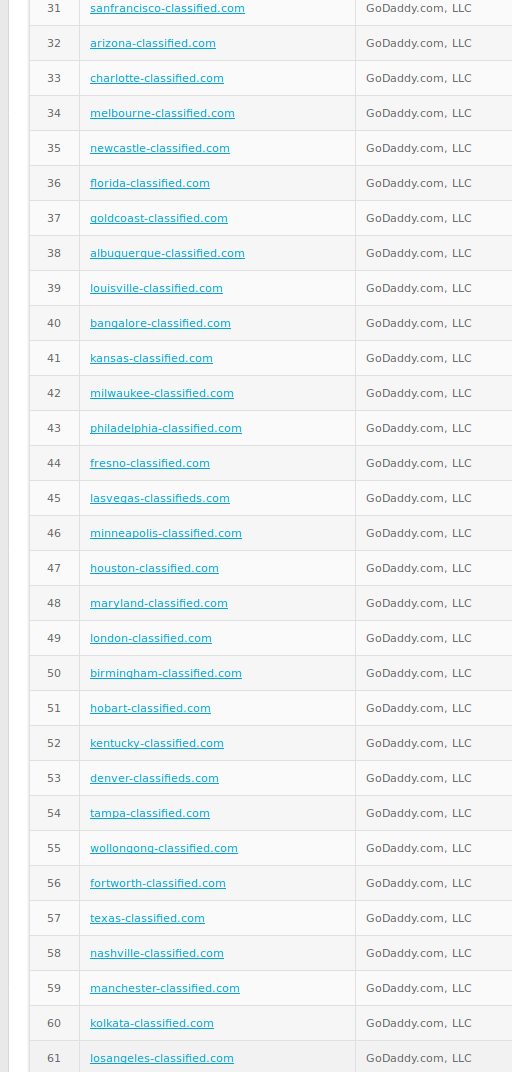
Exhibit C
User singhsomya advertises Bedpage as "top free classified site in USA".
Same user in another post recommends Argalon Technologies as a "leading SEO training company in Indore".

Exhibit D
Their aggressive SEO campaign reveals connection to icracker.com.au. This account named "icracker backpage" and with icracker website as a description, posted jobs advertisements for Argalon Technologies. Another example of connection to bedpage and icracker is a Wordpress blog with ads to above mentioned websites. https://emusoma.wordpress.com/
Exhibit E
Allegedly insider view of postmortem events of backpage, where user explains how he(she?) participated in setting up new backpage like websites and advertise them.
Here is another interesting post related to this situation - https://www.reddit.com/r/afterdarkads_com/comments/eh9rnf/advertising_for_escorts_post_backpage/
Above screenshot describes allegedly "dirty" techniques used to generate more profits by posting fake ads that real people have to compete with.
We already know WHERE - what websites might be responsible for human trafficking, WHO - owns some of the after-backpage clone sites, so let's answer the question WHAT is posted on these sites and HOW to distinguish fake advertisement from real one and potential case of human trafficking.
Diving into content of Bedpage & afterdarkads & eBackpage
Minimalist web design of all of the classified ads sites allow to quickly move between cities, services and list all of the advertisements.
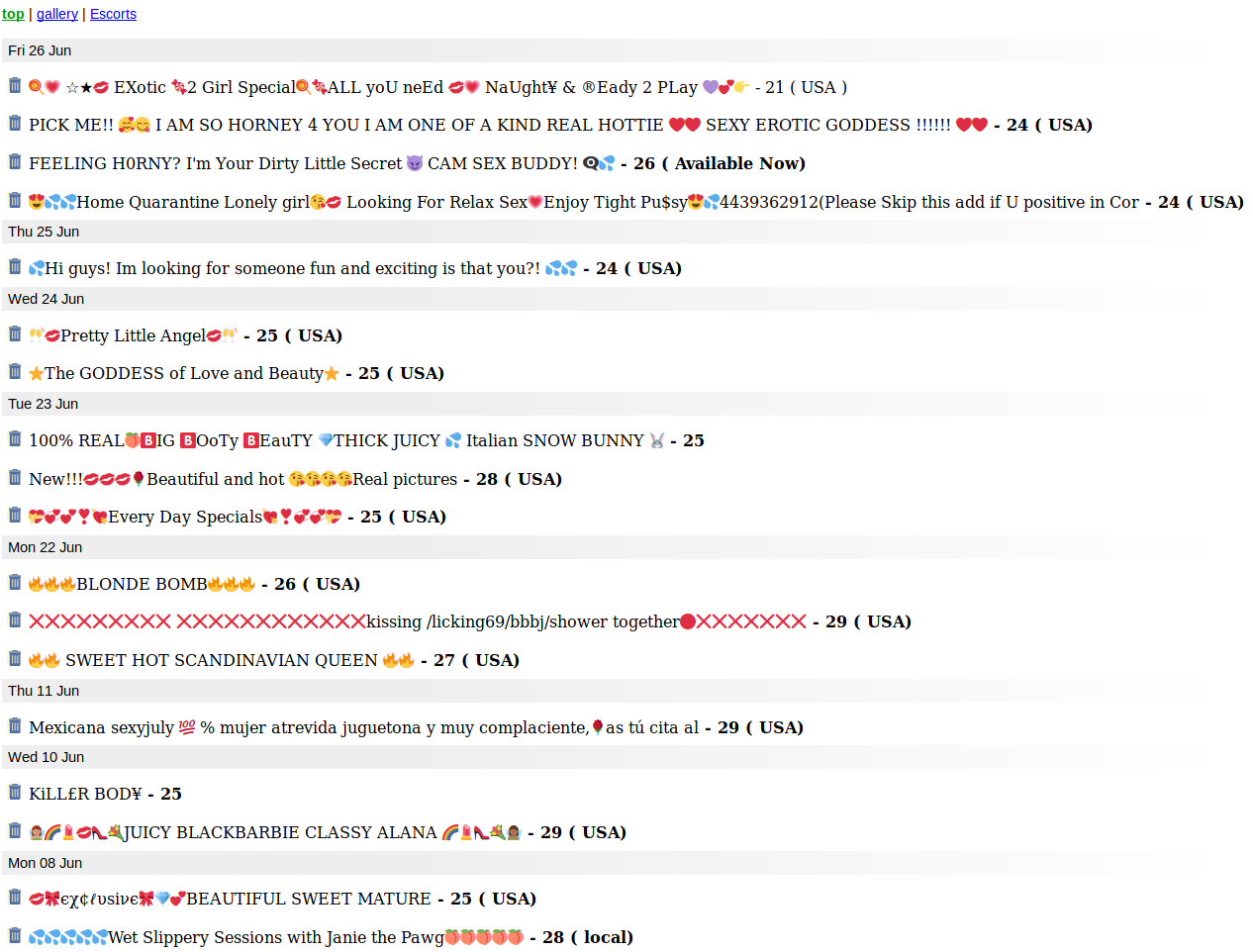
These same ads are posted all over the States and Europe mostly using fake photos without any phone number. And if the number is listed, it is used on different sites and for different cities so I strongly believe it's also fake. You can just google number but remember to put it in quotes for exact search.
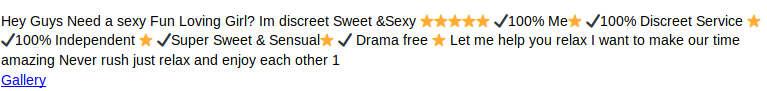
Attached links redirect to adult webcam services, dating websites or even bitcoin related sites. Of course, every link includes referral number/key to get profit from each registered user. I can't say, if ads are being posted by people related to the website, as Reddit user claims, or just by spammers. Both versions though, shows that ebackpage and it's moderators allows spam ads.
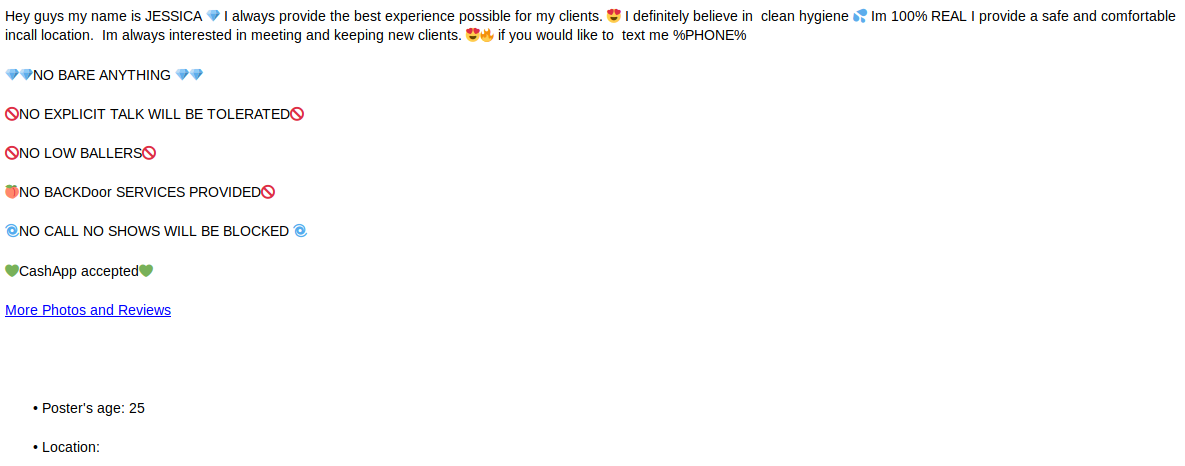
Some ads include phone number indeed, and I came across rating service where users post reviews for escorts with theirs phone numbers. One profile is pure gold. He posts since April 2016 and his last post is dated on 30th of June.
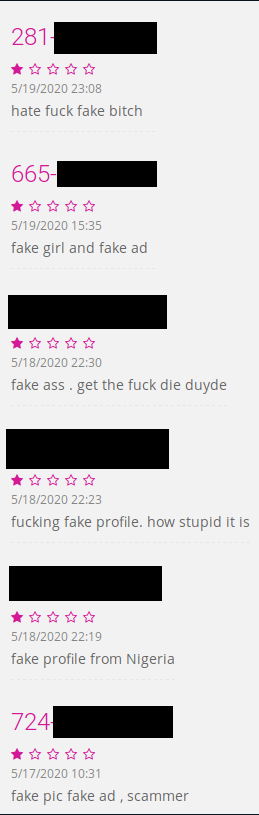
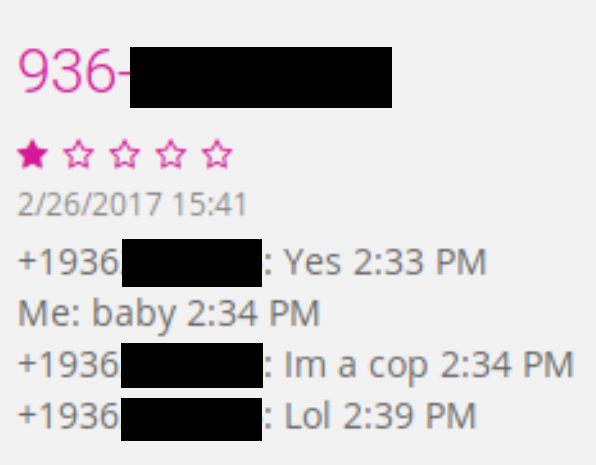
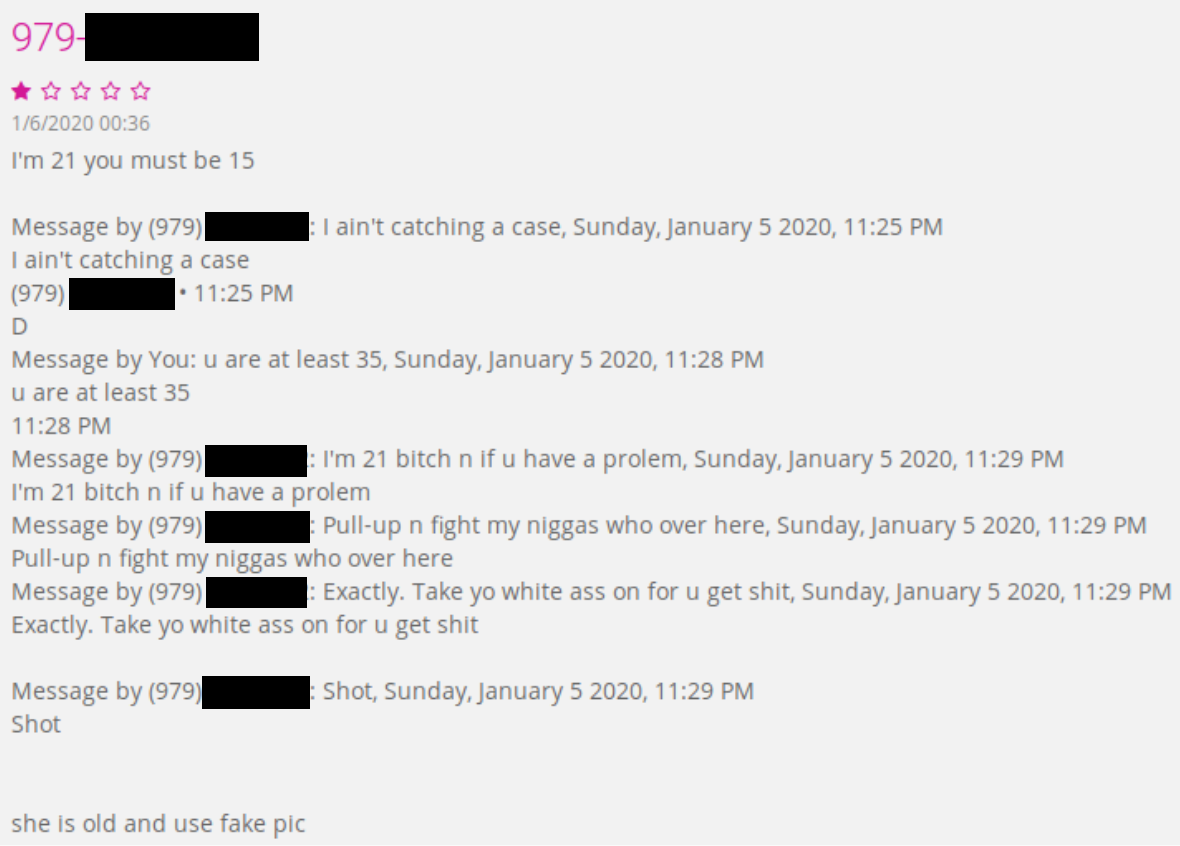
what an adventures this guy has
These people, when contacted, ask for payment in advance or some sort of deposit with use of paypal or bitcoin.
Alexa reveals additional details about the ebackpage, almost 90% of all traffic comes from India.
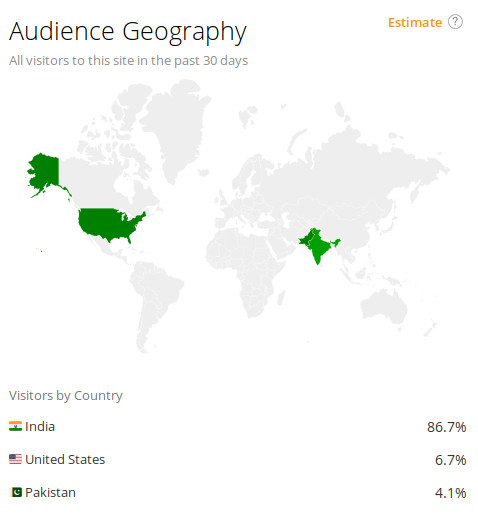

Similar situation applies to afterdarkads despite what Reddit user says in his story - "That's why I liked working with afterdarkads, they at least will not allow fake posters."
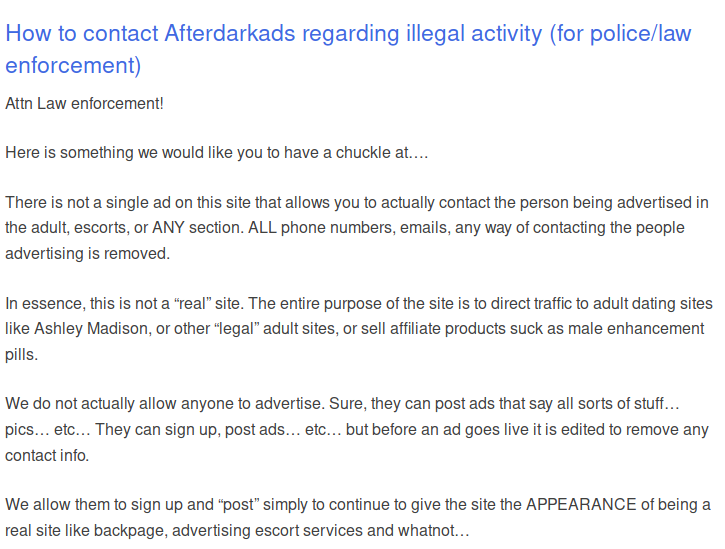
Ads contain links to different sites, (as it was with ebackpage), including Viagra ads but especially to Ashley Madison, as above screen shows.
Interesting fact: Ashley Madison uses domain ashleyrnadison.com (rn instead of m) for advertising. You can read about it in article below.
The Ashley Madison documents you weren’t supposed to see
I did not compare referral links from ebackpage and afterdarkads to establish connection between them but they are allegedly connected through Reddit user and are scams anyway.
Bedpage, from the other hand, is the cleanest site from previously mentioned. I doubt it has any associations with afterdarkads or ebackpage.

To illustrate you a scale of bedpage, imagine that monthly traffic grew from 3.85 million in April, to 4.55 in May, this year, 700k users in a month and during pandemic.
I verified many ads from there, i.e. cross-referenced phone number, email or writing style with other ads posted on different sites. Location and photos matched the person, but I didn't check review though. I saw many people migrated to bedpage from seized bodyrubshop and cityxguide.
Knowing how many spammers and fake ads are on some sites, our main focus will be bedpage. It's on high place in adult category in terms of "escort" and TS (Therapeutic Massages) services.
They most probably already cooperate with law enforcement and NCMEC but they are Switzerland based which makes it harder from jurisdiction perspective, for example subpoenas from US government might not apply to them.
Looking for a sign
Beside law enforcement and child protection agencies, also private companies are engaged in fight with human trafficking online. The most popular company which fight with child exploitation and modern slavery is Thorn co-founded by Ashton Kutcher and Demi Moore.
They implemented "Share Hash Program" which allows quickly respond to the child abuse content online. It's a database of hashes of known images with sexual content that companies can access and block this specific material and share their findings with everyone else.
They also act based on the reports from NCMEC and other companies with help of their task force. Tracking this content it's a complex process from social media to bitcoin transaction and dark net, it's crazy how some criminals groups cooperated with themselves - human trafficker or pedophiles with carders to get money for anonymous hosting or posting ads.
However, in next parts, I want to focus specifically on the backpage like websites and proactive techniques used by Thorn to detect possible cases of human trafficking or underage child exploitation.
You must watch this short movie about how Thorn dealt with this problem on Backpage.
She explains how her program (now used by Thorn) connect various ads to themselves thanks to writing style and tracking bitcoin transactions.
If you take a look on the ads posted on these websites you can easily spot differences and similarities in writing style or emoticons but it's quite an effort to build an algorithm that would do it automatically. It's also probably based on database containing "forbidden words" and example of ads from actual cases of human trafficking.
Each ad contains description, phone number, email and photo. These indicator probably are also examined in order to establish new or ensure existing connections between ads and, at the end, people who posted it.
Timestamps of posted ads allowed to connect bitcoin wallets. Exact time and date is compared with other transaction to backpage and exchanges. There are still websites that offers bitcoin directly to backpage account - buybpcredits or bitquick (both inactive)
In next parts I hope to present how to write proof of concept tool used by Thorn and dive deeper into various cases and websites in this matter.
This episode ends with a plot twist cliffhanger
Is it really undercover operation?
This article mentions a sting in Polk Countr, FL.
For the Backpage Sting Operations in Polk County, FL, the undercover operations are set up at a house in a neighborhood in the northern edge of Polk County in Davenport. The undercover house used in the sting operation was just 1,000 feet south of the Osceola County line just off the I-4 Interstate.
Kudos for person who can geolocate this house.
Summary & What's next?
As I wrote previously, human trafficking is one of the most complex OSINT investigations ever. This article was only an introduction to present history of Backpage and new websites where these activities may occur.
For the next parts, I want to focus on technical capabilities of Thorn - how they respond and detect possible incidents of human trafficking and and how to write tool described in the video.
Presented sites are just drop in the ocean, I want to focus also on other in clearnet as well as darknet, including potentially compromised ones.
Interesting cases, from OSINT perspective, are posted publicly every month or so. I already started small post-mortem investigation of known convicted persons for human trafficking or child abuse and recreated their business and social path, i.e. social media accounts, friends, connections to other groups and possible communication channel.
One of the example is still fresh, dated on 16 June this year, "Operation Guardians of Innocence V". Sheriff Grady Judd is right men on the right place, his speeches are amazing and what's important for us, all details about arrested people are public.
A lot of Disney/Disney World employees have been charged over the years in Polk Country. It's another rabbit hole for someone to investigate.
Unfortunately, I can't afford no longer to write articles in the same way as for first season, so season 2 will be for paid subscribers only, I will explain it more in the summary. I don't know if there is something who read my blog on regular basis and how many people would be interested in next articles so let me know - click reaction at the bottom
like me on Twitter
https://twitter.com/@the_wojciech
or just sign up now
But before that, read summary of season 1 and decide if you want to be part of next one.




